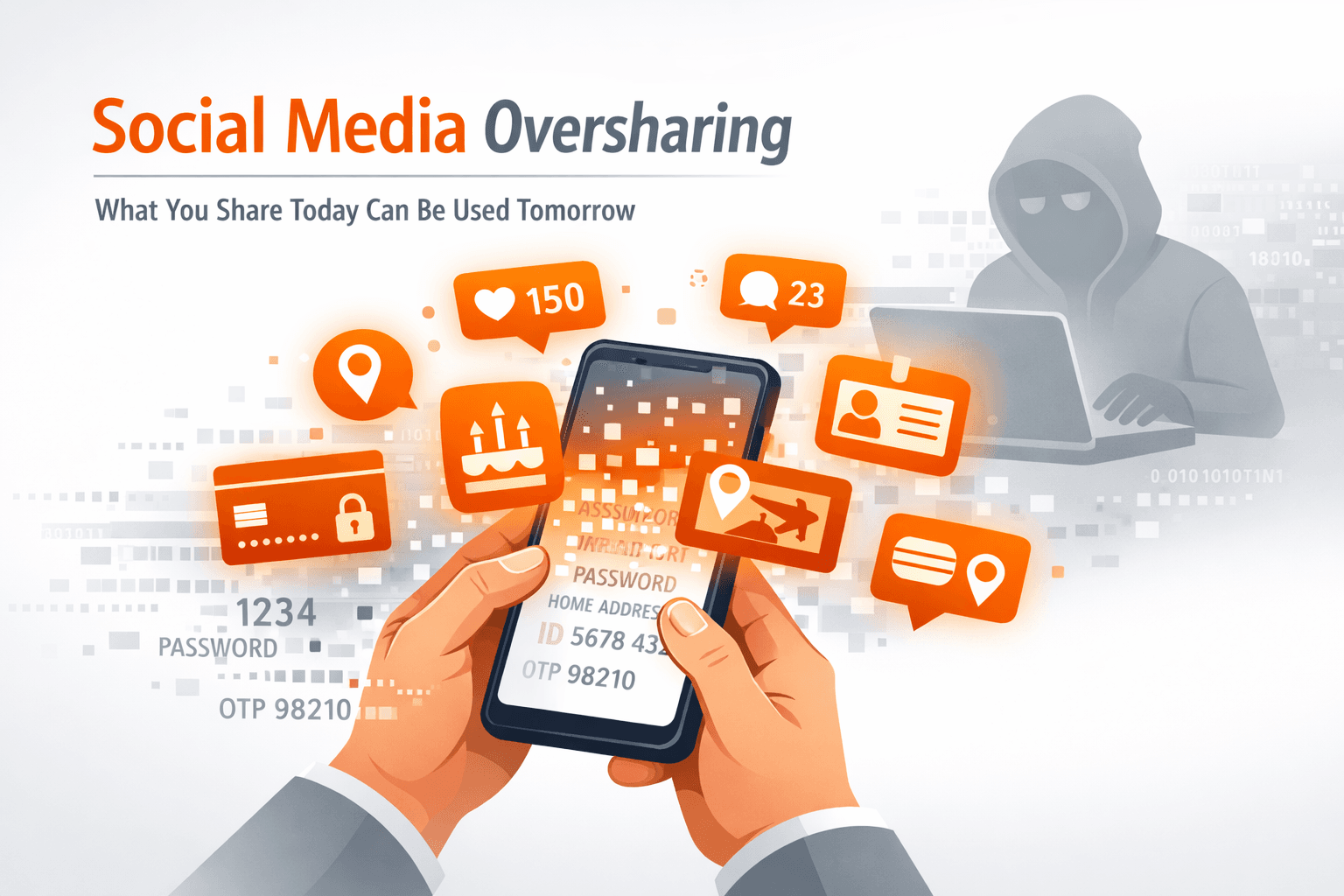
Before attackers hack — they research.
Most cyberattacks today don’t begin with malware. They begin with observation.
Threat actors actively scan LinkedIn, Instagram, X, and other platforms to gather details about individuals and organizations. What looks like a harmless post can become valuable intelligence for phishing, impersonation, and fraud.
Oversharing isn’t just a privacy issue anymore — it’s a cybersecurity risk.
How Oversharing Becomes an Attack Tool
Both individuals and organizations unknowingly provide attackers with context.
Here’s how:
Job updates & tech posts
Sharing tools, systems, or new roles can reveal your company’s tech stack and internal processes — making phishing emails more convincing.
Promotions & org changes
Public reporting structures help attackers impersonate managers or executives in Business Email Compromise (BEC) scams. Social Media
Travel & routine updates
Posting travel plans or live locations can expose timing gaps for fraud or impersonation.
Screenshots & work photos
Dashboards, badges, internal emails, and background screens can leak sensitive operational information.
Vendor & partnership announcements
Attackers can pose as third-party vendors and send realistic payment or access requests.
What feels like engagement and networking may become reconnaissance material.
Why This Matters for Everyone
For Individuals:
Oversharing increases the chance of:
- Targeted phishing
- Identity theft
- Account takeover
- Professional impersonation
For Organizations:
Public employee information expands the “human attack surface.” The more context attackers have, the more personalized — and successful — their attacks become.
Cybercriminals don’t guess anymore. They research.
What You Can Do
As an Individuals:
Review your privacy settings Avoid sharing internal tools or sensitive work details Be cautious with travel and routine updates Think before posting screenshots
As an Organizations:
Include social media risks in security awareness training Create clear posting guidelines for employees Monitor executive and brand visibility risks Conduct periodic digital footprint reviews
Security today extends beyond firewalls — it includes what’s publicly visible online.
Before posting, ask yourself:
“If someone wanted to impersonate me or target my organization, could this information help them?”
Cybersecurity isn’t just about protecting systems. It’s about protecting context.
And awareness is your strongest first defense.