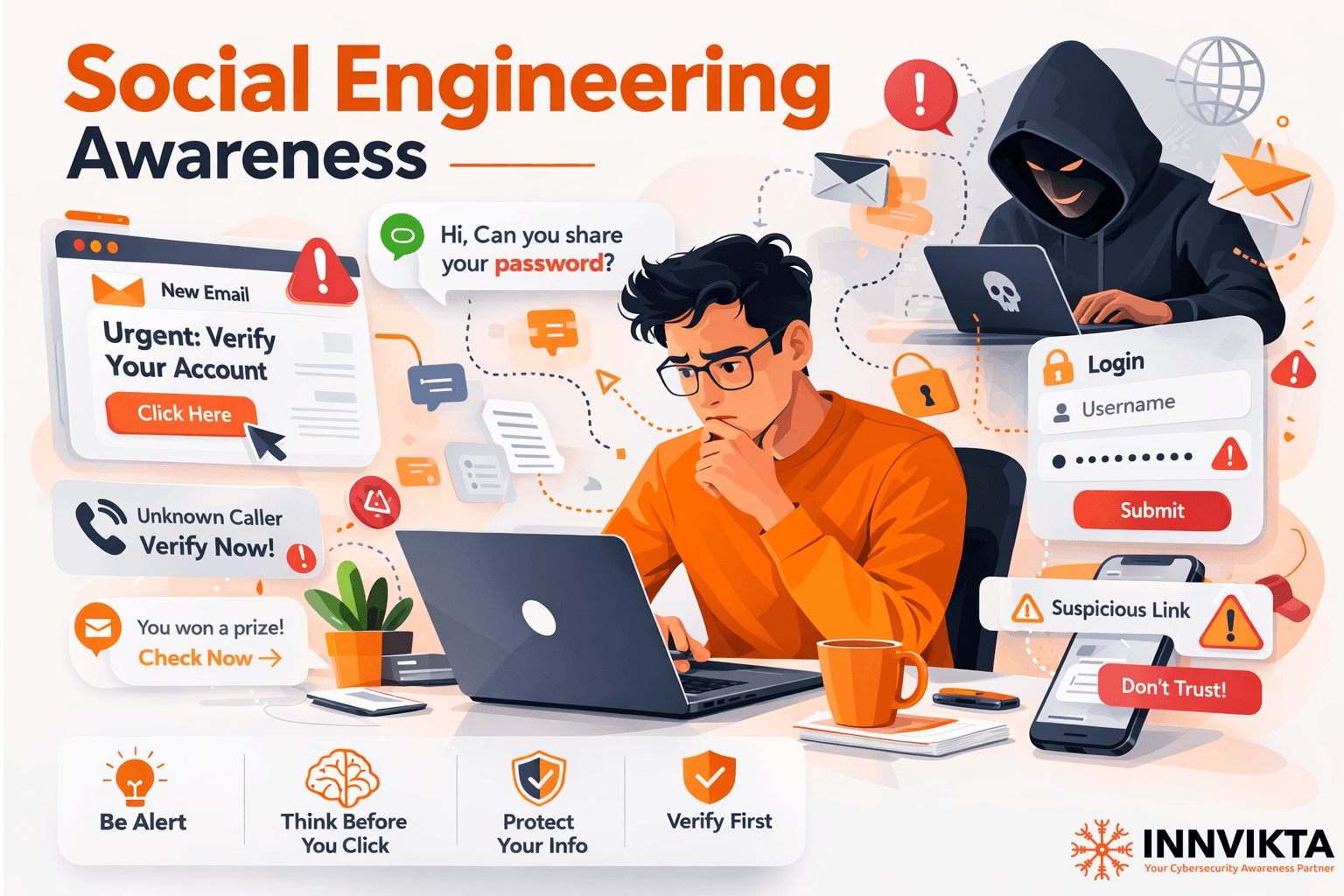
Hackers Don’t Break Into Systems – They Manipulate People.
Imagine starting your workday and receiving a message from your CEO asking for an urgent payment approval.Another employee receives an email from IT saying their password will expire within the next 10 minutes unless they reset it immediately.
Meanwhile, someone in HR downloads what appears to be a resume from a job applicant.Everything seems routine.But in reality, none of these interactions are legitimate.
They are carefully crafted social engineering attacks designed to manipulate human behavior.
Modern cyber attackers have realized something important:
They don’t need to break through complex security systems when they can simply convince someone inside the organization to open the door for them.
This is why social engineering has become one of the most dangerous cybersecurity threats today.
Why Social Engineering Works
Most cybersecurity strategies focus on technology:
Firewalls
Endpoint protection
Network monitoring
But attackers focus on something different.
Human psychology.
They exploit emotions like:
• Trust
• Urgency
• Fear
• Curiosity
• Authority
And when an employee reacts without verifying the situation, attackers gain access to systems, data, and finances.
Understanding these tactics is the first step in defending against them.
Let’s explore the top 10 social engineering techniques hackers commonly use.
1.Phishing
Phishing is the most widespread social engineering technique.
Attackers send emails that appear to come from trusted sources such as banks, company leadership, or IT teams.
The message usually encourages the victim to:
• Click a malicious link
• Download an infected attachment
• Enter login credentials on a fake website
Even a single phishing email can lead to credential theft or network compromise.
This is why organizations increasingly deploy phishing simulation platforms like Innvikta’s to train employees to recognize and report suspicious emails before real attackers succeed.
2.Spear Phishing
Unlike traditional phishing campaigns sent to thousands of users, spear phishing targets specific individuals.
Attackers gather information from sources such as:
• LinkedIn profiles
• Company websites
• Social media posts
Using this information, they craft highly convincing messages tailored to the victim.
These personalized attacks have a much higher success rate.
3.Business Email Compromise (BEC)
In a BEC attack, hackers impersonate executives or senior management.
For example, a finance employee might receive a message appearing to come from the CEO requesting an urgent payment or vendor transfer.
Because the request appears legitimate and urgent, employees may process the transaction without verification.
Globally, BEC attacks have resulted in billions of dollars in financial losses.
4.Pretexting
Pretexting involves creating a fabricated story to convince victims to reveal sensitive information.
Attackers may pretend to be:
• IT support staff
• Bank representatives
• Government officials
• Internal auditors
The victim believes they are helping a legitimate request and unknowingly shares confidential data.
5.Baiting
Baiting exploits curiosity.
Attackers provide something enticing that encourages victims to interact with it.
Examples include:
• USB drives labeled “Confidential Salary Data”
• Free software downloads • Giveaway links
Once accessed, the bait installs malware or steals sensitive information.
6.Quid Pro Quo
In quid pro quo attacks, the attacker offers something in exchange for information.
For instance, someone may call employees pretending to be IT support offering help with a technical issue.
In return, they ask the employee to provide login credentials or install software.
The victim believes they are receiving assistance when in reality they are enabling the attack.
7.Tailgating
Tailgating is a physical social engineering technique.
An attacker follows an authorized employee into a restricted building or office area.
Employees often hold doors open out of courtesy without verifying identity.
Once inside, attackers may access computers, internal networks, or sensitive documents.
8.Vishing
Vishing, or voice phishing, occurs through phone calls.
Attackers impersonate trusted entities such as banks, customer support teams, or company IT departments.
They create urgency and pressure victims to disclose sensitive information such as:
• OTP codes
• Account details
• Login credentials
9.Smishing
Smishing uses SMS or messaging apps to conduct phishing attacks.
Victims receive messages like:
“Your bank account has been locked. Click here to verify.”
or
“Package delivery failed. Update your address.”
These messages contain malicious links leading to fake websites designed to steal credentials.
10.Scareware
Scareware manipulates fear.
Victims see alarming messages claiming their device is infected with malware.
They are urged to download software that supposedly fixes the problem.
In reality, the software itself installs malware or steals sensitive data.
Turning Employees Into the First Line of Defense
The reality is simple.
Cyber attackers understand that people are often easier to manipulate than technology.
This is why organizations must move beyond traditional security tools and focus on human risk management.
At Innvikta, we help organizations strengthen their security awareness and resilience against social engineering attacks through:
– Realistic phishing simulations
-Security awareness training
-Behavioral risk analytics
-Continuous employee education
By exposing employees to simulated attacks in a safe environment, Innvikta helps organizations build awareness before real attackers strike.
Cybersecurity is no longer just a technical challenge.
It is a human challenge.
The organizations that succeed in defending against modern threats are the ones that train their people to recognize manipulation before it turns into a breach.
And in today’s threat landscape, awareness is not optional.
It is essential.
Which social engineering technique do you think is the most effective against organizations today?